25 min read
Maritime Cyber Security & Threats 25 Apr - May 21
By: Dryad Global on May 4, 2021 at 9:28 AM
Dryad and cyber partners RedSkyAlliance continue to monitor attempted attacks within the maritime sector. Here we continue to examine how email is used to deceive the recipient and potentially expose the target organisations.
"Fraudulent emails designed to make recipients hand over sensitive information, extort money or trigger malware installation on shore-based or vessel IT networks remains one of the biggest day-to-day cyber threats facing the maritime industry."
Dryad Global's cyber security partners, Red Sky Alliance, perform weekly queries of backend databases, identifying all new data containing Motor Vessel (MV) and Motor Tanker (MT) in the subject line of malicious emails. Email subject line Motor Vessel (MV) or Motor Tanker (MT) keyword usage is a common lure to entice users in the maritime industry to open emails containing malicious attachments.
 With our cyber security partner we are providing a weekly list of Motor Vessels where it is observed that the vessel is being impersonated, with associated malicious emails.
With our cyber security partner we are providing a weekly list of Motor Vessels where it is observed that the vessel is being impersonated, with associated malicious emails.
The identified emails attempted to deliver malware or phishing links to compromise the vessels and/or parent companies. Users should be aware of the subject lines used and the email addresses that are attempting to deliver the messages.
Those who work in the security industry can quickly identify the suspicious aspects of these emails, but the targets often cannot. Even if attackers can only get 10% of people to open their malicious email attachments, they can send thousands out in a day using similar templates resulting in hundreds of victims per day. They can also automate parts of this process for efficiency. It is critical to implement training for all employees to help identify malicious emails/attachments. This is still the major attack vector for attackers looking to attack a network. These analytical results illustrate how a recipient could be fooled into opening an infected email. They also demonstrate how common it is for attackers to specifically target pieces of a company’s supply chain to build up to cyber-attacks on the larger companies. Doing so could cause the recipient to become an infected member of the maritime supply chain and thus possibly infect victim vessels, port facilities and/or shore companies in the marine, agricultural, and other industries with additional malware.
Malicious Email collection 25 Apr - 2 May 21
|
First Seen |
Subject Line Used |
Malware Detections |
Sending Email |
Targets |
|
Apr 25, 2021 |
port inquire - PDA n port info - load abt 55k clinker in bulk |
W32/MSIL_Kryptik.DYY.gen!Eldorado |
"joey@safeocean.com.cn" 280ed@20de95bfb5157.cn |
20de95bfb5157.cn |
|
Apr 25, 2021 |
MV WAN TONG 18 - FRT PAYMENT |
Trojan:Win32/Wacatac.B!ml |
“opshdy” bcd4142@3c1594bc.com |
3c1594bc.com |
|
Apr 25, 2021 |
MV SPAR CANIS--Loadg Port Agent Nomination |
Trojan:Win32/AgentTesla!ml |
"shipping8888@188.com" dfa6d55d059@679.com |
1b84072c33545fa2e.com |
|
Apr 25, 2021 |
MV English Bay - Inquiry 193-2020-SP0087-B(01) ++REMINDER++ |
Trojan:Win32/AgentTesla!ml |
"opeMandy Ho" pacificbasin-technical@gl-es.com |
gl-es.com |
|
Apr 25, 2021 |
MV Koombana Bay - Inquiry 215-2020-SP0066-B(01) |
Trojan:Win32/AgentTesla!ml |
“ME” pacificbasin-technical@gl-es.com |
gl-es.com |
|
Apr 25, 2021 |
(KOREA SHIPPING - KLCSM) |
Trojan:Win32/AgentTesla!ml |
"Park Jung-ho" 830@7cede0c1.kr |
Targets Not Disclosed |
|
Apr 25, 2021 |
MV EUNICE - Agency Appointment & EPDA Inquiry |
HEUR:Trojan-PSW.MSIL.Agensla.gen |
“opshk” a522b9@f925e2623c9.com |
f925e2623c9.com |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” 9f9@b682da816863.br |
c973eadbb8f9b.biz |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” 9f9@b682da816863.br |
d7591795dda69ac9a1b.com |
|
Apr 25, 2021 |
Shipping documents notice. |
HTML/Infected.WebPage.Gen2 |
“EBILLS” 9f9@b682da816863.br |
a8871.com |
|
Apr 25, 2021 |
Shipping documents notice. |
HTML/Infected.WebPage.Gen2 |
“EBILLS” 9f9@b682da816863.br |
2854063a17.com |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” e3afe@90c149405390bc.cn |
5db65b7c3fe.com |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” e3afe@90c149405390bc.cn |
9edbfdd92aed82.com |
|
Apr 25, 2021 |
Shipping documents notice. |
HTML/Infected.WebPage.Gen2 |
“EBILLS” 9f9@b682da816863.br |
60a459f1d8.com |
|
Apr 25, 2021 |
Shipping Documents-BL#SE20100078/001 |
Exploit:O97M/CVE-2017-11882.HDY!MTB |
"Shanghai Ming Wah Shipping Co., Ltd" eka.wati@hinet.co.id |
Targets Not Disclosed |
|
Apr 25, 2021 |
DHL Description: SHIPPING DOCUMENTS, ETC DOC |
Exploit:Win32/CVE-2017-11882!ml |
lekside@futurenetqy.com |
tidlo.lt |
|
Apr 25, 2021 |
PDA |
W32/Heuristic-200!Eldorado |
“Aiden Chan” aidenletzgo@gmail.com |
kyec.com.tw |
|
Apr 25, 2021 |
pda |
HEUR.ExecInMail |
bc_m_choco@hotmail.com |
kyec.com.tw |
|
Apr 25, 2021 |
FACTURA - Env\xedo electr\xf3nico de Comprobante Fiscal Digital (438826) |
Troj/Phish-JBG |
“Servicio Seguro de Entrega de CFDI” a26d7311@ff76befd6c73d81600c.mx |
d6fcd.net |
|
Apr 25, 2021 |
Shipping Documents-BL#SE20100078/001 |
Exploit:O97M/CVE-2017-11882.HDY!MTB |
"Shanghai Ming Wah Shipping Co., Ltd" eka.wati@hinet.co.id |
Targets Not Disclosed |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” 2c4be6a@0a5031072ef6.com |
0023e3a6.net |
|
Apr 25, 2021 |
Shipping documents notice. |
HTML/Phish.78C3!tr |
“EBILLS” 2c4be6a@0a5031072ef6.com |
8493fa9ba42.com |
|
Apr 25, 2021 |
Shipping documents notice. |
HTML/Phish.78C3!tr |
“EBILLS” 2c4be6a@0a5031072ef6.com |
5c4852a79b845.il |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” 2c4be6a@0a5031072ef6.com |
a076f4c2d.net |
|
Apr 25, 2021 |
Documents Of Shipping |
Trojan:Win32/Woreflint.A!cl |
"DHL International GmbH" efe1e7ac07ca3478@887.com |
c4e30fc94334d457cb.uk |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” dpartin@singerlevick.com |
aiyos.com |
|
Apr 25, 2021 |
Draft BL//Extra Pick-up Fee//Update Vessel |
Trojan:MSIL/AgentTesla!MTB |
“Angelina Dacosta” Angelina.Dacosta@craneww.com |
electroputere.ro |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” 9869b@0ac0271.jp |
63477882ea284c.au |
|
Apr 25, 2021 |
Port agency appointment -MV/BBC NILE/ 1113043/ |
Trojan:Win32/AgentTesla!ml |
"liufei@winlucky.com.cn" 6707285@bf5f566bbbb0.cn |
bf5f566bbbb0.cn |
|
Apr 25, 2021 |
MV KEY INTEGRITY / Acc Langlois - Discharging / Agency appointment & PDA |
Trojan:Win32/AgentTesla!ml |
"operations" f7235a61f@9d52f75c.gr |
9d52f75c.gr |
|
Apr 25, 2021 |
M.V //DA TONG YUN VOY// AGENCY NOMINATION FOR DISCHARGING WHEAT |
Trojan:Win32/AgentTesla!ml |
"Cosco Shipping Specialized Carriers Co" 33e8@6a68cebaf9.cn |
6a68cebaf9.cn |
|
Apr 25, 2021 |
Re: Re: MV SKY HEIGHT/FN |
Program:Win32/Uwamson.A!ml |
"james@seaconshipping.com" aa2d@2817aa0b22b13b.com |
2817aa0b22b13b.com |
|
Apr 25, 2021 |
MV OLYMPIC PRIDE / SEACON ENTERPRISE PTE LTD CP DD 05.03.2021 |
Trojan:Win32/AgentTesla!ml |
"Ursa Shipbrokers" ba19a09a68@a02b.gr |
a02b.gr |
|
Apr 25, 2021 |
Shipping documents notice. |
HEUR:Trojan.Script.Generic |
“EBILLS” 3f9633@a0e32fb.com |
a0c170b93efd5e.au |
|
Apr 25, 2021 |
SPAM: SHIPPING DOCUMENT |
Trojan:Win32/VBInject.VAMV!MTB |
“Shanghai Xing Yang Shipping Co., Ltd” d7a6d@bb6a95ce6.cn |
85441484b.it |
|
Apr 25, 2021 |
PO 7365 and Duluth Seaway Port Authority Proposal |
DOC/Phishing.Agent.TA |
"Dean Lembke" dlembke@duluthport.com |
duluthport.com |
|
Apr 25, 2021 |
LX MARINE SPARE PARTS |
Exploit:O97M/CVE-2017-11882.DR!MTB |
"LX MARINE CO.,LTD" danus.hamid@hinet.co.id |
Targets Not Disclosed |
|
Apr 25, 2021 |
M/T. YUAN JU WAN EPDA AND PORT INFO REQUEST |
Exploit.CVE-2018-0802.Gen |
“COSCO SHIPPING TANKER(Singapore) PteLtd” ops@csdvlp.com.sg |
planasia.com |
|
Apr 25, 2021 |
M/T. YUAN JU WAN EPDA AND PORT INFO REQUEST |
Exploit.CVE-2018-0802.Gen |
“COSCO SHIPPING TANKER(Singapore) PteLtd” e84@11fcfb6d27.sg |
3a9b370c66a5e.com |
|
Apr 25, 2021 |
KING SAIL CTM ARRANGEMENT |
Trojan:Win32/Wacatac.B!ml |
"zsship@shipping.sinosteel.com" 5d92aea@e6a360508ff2bca380.com |
e6a360508ff2bca380.com |
|
Apr 25, 2021 |
MV.GRACE OCEAN // 1st hire soa (resend) |
Trojan:Win32/Woreflint.A!cl |
"MIT OPS TEAM" <53630@dfe51de878.tw> |
dfe51de878.tw |
|
Apr 25, 2021 |
MV JACARANDA MAY/ CALL FOR DSG ABT 15000MT PKE IN BULK |
Trojan:Win32/Woreflint.A!cl |
"osd" 095fc82@8f06d6c40b.net |
8f06d6c40b.net |
|
Apr 25, 2021 |
MV JOIE N L / 1st hire statement |
Trojan:Win32/Woreflint.A!cl |
"Capt. VC Duan" dca6135@3c1594bc.com |
3c1594bc.com |
|
Apr 25, 2021 |
ENQUIRY // MV CSC RONG HAI LOADING OPERATION |
Trojan:Win32/Woreflint.A!cl |
"linyunzi@cmhk.com" 327569849@9395.com |
9395.com |
|
Apr 25, 2021 |
DHL Express shipping confirmation |
Trojan:MSIL/AgentTesla.NK!MTB |
“DHL EXPRESS” alfredo.soria@dhl.com |
Targets Not Disclosed |
|
Apr 25, 2021 |
WG: Commercial Invoice & Bill Of lading, Packing List |
Trojan:Script/Phonzy.B!ml |
“Postverteiler” pm@hoffmanneitle.com |
hoffmanneitle.com |
|
Apr 25, 2021 |
ACHTUNG: geblockter Dateianhang Re: Commercial Invoice & Bill Of\r\n lading, Packing List |
Trojan:Script/Phonzy.B!ml |
“Bernard Pang” u00a0febjobs@applianceworld.co.ug |
welser.com |
|
Apr 25, 2021 |
INVOICE PAYMENT/ SHIPPING DOCUMENT |
Trojan:Win32/Phonzy.B!ml |
“ACCOUNT PAYABLE” j.pidd@hotmail.com |
fabrimat.fr |
|
Apr 25, 2021 |
FedEx ONLINE SHIPPING PARCEL ARRIVAL NOTIFICATION DATED 30TH APRIL |
Trojan:Win32/Wacatac.B!ml |
“FeDEx OFFICE” info@123edeerty.ga |
Targets Not Disclosed |
|
Apr 25, 2021 |
ENC: Nova Reserva - Booking Engine |
Exploit.CVE-2017-0199.Gen |
caf9@97cd5f8e446.com |
a01920e188.org |
|
Apr 25, 2021 |
WG: Commercial Invoice & Bill Of lading, Packing List |
Trojan:Script/Phonzy.B!ml |
“Postverteiler” pm@hoffmanneitle.com |
hoffmanneitle.com |
|
Apr 25, 2021 |
ESTADO DEL PEDIDO RO 12094 || PF-2021430 || LCL FOB ALEMANIA |
Gen:Mail.Nophy.2 |
"Inge Lise Falkenskov-Habicht" admin@previousmail.host |
indra.es |
In the above collection, we see malicious actors attempting to use vessel names to try to spoof companies in the maritime supply chain. This week we observed a wide variety of maritime-related subject lines. Some of the new vessel names used this week include “MV Spar Canis” and “MV Grace Ocean” among others. There appears to be an ongoing campaign using the same subject line to target numerous recipients.
Analysts observed threat actors impersonating multiple companies to spread phishing malware while using the same subject line – “Shipping documents notice.” While obfuscation of the sending email makes identification of the true sender more difficult, analysts observed at least one sender email listed in original form allowing analysts to identify one of the companies being impersonated in this campaign. The sending email in one case appeared as “EBILLS<dpartin@singerlevick[.]com>” indicating the attacker is trying to impersonate the legal firm Singer & Levick, based out of Dallas, TX USA.
It appears that attackers are spoofing the sending email and are not using a compromised account. However, the email address belonging to a lead attorney at the company is listed in the recent COMB (Combination of many breaches) breach data. Through the compromise of legitimate business email credentials, attackers can login to real accounts appearing more legitimate, and leading to a higher rate of success. The following obfuscated email addresses were used to send malware:
- “EBILLS” 2c4be6a@0a5031072ef6.com (“EBILLS”
dpartin@singerlevick.com)
- “EBILLS” e3afe@90c149405390bc.cn
- “EBILLS” 9f9@b682da816863.br
- “EBILLS” 9869b@0ac0271.jp
- “EBILLS” 3f9633@a0e32fb.com
The attackers are using the alias “EBILLS” to make the target think the email is coming from a legitimate online service. Although the sending emails are mostly obfuscated, the TLD’s used indicate the attackers are impersonating senders from Japan, Brazil, China, and likely the United States. Because the message body is “[redacted]” there is no additional information in the message body to help identify the attackers.
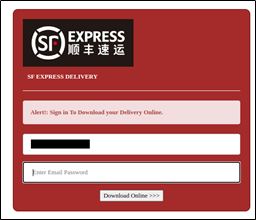
There are more than 15 unique email addresses being targeted by these malicious emails. If any of the targets opened the malicious attachment, they would be prompted to input their password into a fake login screen created by the attackers.
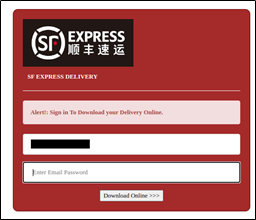
Image of fake login screen created by attackers to steal credentials
After the target inputs their password (username is pre-filled by attackers), the attackers would steal this password for use in future cyber-attacks. All of the phishing links observed appear to spoof a login for SF Express Delivery, a common delivery tracking service. Companies who use this software should be aware of this threat and should monitor incoming emails for these patterns.
These analytical results illustrate how a recipient could be fooled into opening an infected email. They also demonstrate how common it is for attackers to specifically target pieces of a company’s supply chain to build up to cyber-attacks on the larger companies. Doing so could cause the recipient to become an infected member of the maritime supply chain and thus possibly infect victim vessels, port facilities and/or shore companies in the marine, agricultural, and other industries with additional malware.
These analytical results illustrate how a recipient could be fooled into opening an infected email. They also demonstrate how common it is for attackers to specifically target pieces of a company’s supply chain to build up to cyber-attacks on the larger companies. Doing so could cause the recipient to become an infected member of the maritime supply chain and thus possibly infect victim vessels, port facilities and/or shore companies in the marine, agricultural, and other industries with additional malware
Fraudulent emails designed to make recipients hand over sensitive information, extort money or trigger malware installation on shore-based or vessel IT networks remains one of the biggest day-to-day cyber threats facing the maritime industry. These threats often carry a financial liability to one or all those involved in the maritime transportation supply chain. Preventative cyber protection offers a strong first-line defence by preventing deceptive messages from ever reaching staff inboxes, but malicious hackers are developing new techniques to evade current detection daily. Using pre-emptive information from Red Sky Alliance-RedXray diagnostic tool, our Vessel Impersonation reports, and Maritime Blacklists offer a proactive solution to stopping cyber-attacks. Recent studies suggest cyber-criminals are researching their targets and tailoring emails for staff in specific roles. Another tactic is to spoof emails from the chief executive or other high-ranking maritime contemporaries in the hope staff lower down the supply chain will drop their awareness and follow the spoofed email obediently. Analysts across the industry are beginning to see maritime-specific examples of these attacks.
Pre-empt, don't just defend
Preventative cyber protection offers a strong first-line defense by preventing deceptive messages from ever reaching staff inboxes, but malicious hackers are developing new techniques to evade current detection daily. Using preemptive information from Red Sky Alliance RedXray diagnostic tool, our Vessel Impersonation reports and Maritime Blacklists offer a proactive solution to stopping cyber-attacks. Recent studies suggest cyber-criminals are researching their targets and tailoring emails for staff in specific roles. Another tactic is to spoof emails from the chief executive or other high-ranking maritime contemporaries in the hope staff lower down the supply chain will drop their awareness and follow the spoofed email obediently. Analysts across the industry are beginning to see maritime-specific examples of these attacks.
The more convincing an email appears, the greater the chance employees will fall for a scam. To address this residual risk, software-based protection should be treated as one constituent of a wider strategy that also encompasses the human-element as well as organizational workflows and procedures.
It is imperative to:
- Train all levels of the marine supply chain to realize they are under constant cyber-attack.
- Stress maintaining constant attention to real-world cyber consequences of careless cyber practices or general inattentiveness.
- Provide practical guidance on how to look for a potential phishing attempt.
- Use direct communication to verify emails and supply chain email communication.
- Use Red Sky Alliance RedXray proactive support, our Vessel impersonation information and use the Maritime Black Lists to proactively block cyber attacks from identified malicious actors.
Related Posts
Maritime Cyber Security & Threats December Week 2
Dryad and cyber partners RedSkyAlliance continue to monitor attempted attacks within the maritime..
Maritime Cyber Security & Threats Sep 2020 Week..
Dryad and cyber partners RedSkyAlliance continue to monitor the stark upward trend in attempted..
Maritime Cyber Security & Threats Sep 2020 Week..
Dryad and cyber partners RedSkyAlliance continue to monitor the stark upward trend in attempted..





