22 min read
Maritime Cyber Security & Threats Feb -March 2021
By: Dryad Global on March 22, 2021 at 9:38 AM

Dryad and cyber partners RedSkyAlliance continue to monitor attempted attacks within the maritime sector. Here we continue to examine how email is used to deceive the recipient and potentially expose the target organisations.
"Fraudulent emails designed to make recipients hand over sensitive information, extort money or trigger malware installation on shore-based or vessel IT networks remains one of the biggest day-to-day cyber threats facing the maritime industry."
Dryad Global's cyber security partners, Red Sky Alliance, perform weekly queries of backend databases, identifying all new data containing Motor Vessel (MV) and Motor Tanker (MT) in the subject line of malicious emails. Email subject line Motor Vessel (MV) or Motor Tanker (MT) keyword usage is a common lure to entice users in the maritime industry to open emails containing malicious attachments.
 With our cyber security partner we are providing a weekly list of Motor Vessels where it is observed that the vessel is being impersonated, with associated malicious emails.
With our cyber security partner we are providing a weekly list of Motor Vessels where it is observed that the vessel is being impersonated, with associated malicious emails.
The identified emails attempted to deliver malware or phishing links to compromise the vessels and/or parent companies. Users should be aware of the subject lines used and the email addresses that are attempting to deliver the messages.
Those who work in the security industry can quickly identify the suspicious aspects of these emails, but the targets often cannot. Even if attackers can only get 10% of people to open their malicious email attachments, they can send thousands out in a day using similar templates resulting in hundreds of victims per day. They can also automate parts of this process for efficiency. It is critical to implement training for all employees to help identify malicious emails/attachments. This is still the major attack vector for attackers looking to attack a network. These analytical results illustrate how a recipient could be fooled into opening an infected email. They also demonstrate how common it is for attackers to specifically target pieces of a company’s supply chain to build up to cyber-attacks on the larger companies. Doing so could cause the recipient to become an infected member of the maritime supply chain and thus possibly infect victim vessels, port facilities and/or shore companies in the marine, agricultural, and other industries with additional malware.
Malicious Email collection 8 Feb- 4 Mar 21
|
First Seen |
Subject Line Used |
Malware Detections |
Sending Email |
Targets |
|
Feb 8, 2021 |
MV AQUA SPLENDOR // PORT AGENCY APPOINTMENT |
Trojan:MSIL/AgentTesla.MTR!MTB |
"Jason Ho ISS-China" Jason_Ho@iss-shipping.com |
iss-shipping.com |
|
Feb 8, 2021 |
WG: 52196719 - Feuerschaden Erbengemeinschaft Scheu, Neuweiler\r\n Straße 190, 72461 Albstadt - 18513/ms-msc |
HEUR:Trojan.MSOffice.SAgent.gen |
“Monja Schmitt - THEES+PARTNER Beratende Ingenieure PartGmbB” monja.schmitt@thees.de |
thees.de |
|
Feb 8, 2021 |
MV CAPE SUN-CTM ENQUIRY UMSD49, 000 - AGENT ARRANGEMENT with ETA 26-Jan-20210 |
PWS:MSIL/DarkStealer.AD!MTB |
“Huang Feizhou” sscrm@cmhk.com
|
cmhk.com |
|
Feb 8, 2021 |
PDA REQUEST |
Program:Win32/Wacapew.C!ml |
“Iliyan Stoyanov INTERTRANS” caf9@dec.com |
7925b11e0f.com |
|
Feb 9, 2021 |
REQUEST FOR TRANSFER OF CONTAINER NO FFAU6279595510 |
TrojanDownloader:O97M/Powdow.SWM!MTB |
support@tuchalsadikhairhai.digital |
ilfa.de |
|
Feb 9, 2021 |
RE: Documents Attached for New Sea Shipment//Nastah FCL//20-21/MIL/238 |
Trojan:MSIL/AgentTesla.KO!MTB |
“Mit_freundlichen üß.” 10658788@thyssenkrupp.com |
Targets Not Disclosed |
|
Feb 9, 2021 |
Re: RE: DOORMOVE CONTAINER QUESTIONS MBL SMLMSEL0F0333200 CTNR CAIU6468623 |
TrojanDownloader:O97M/Qakbot.RVC!MTB |
huseyin.donmez@inanplastics.com |
smlines.com |
|
Feb 9, 2021 |
Re: SMQT2006E // HAZMAT CARGO -SEL0D0126700 REMINDER *** // USSEA |
TrojanDownloader:O97M/Qakbot.RVC!MTB |
plapointe@camionsdenislussier.com |
smlines.com |
|
Feb 9, 2021 |
Ocean Freight Payment Notification Of 01_27_2021 |
TrojanDownloader:O97M/Dridex.SS!MTB |
postmaster@vince.com |
mail-relay.msc.com |
|
Feb 10, 2021 |
RE: Documents Attached for New Sea Shipment//Nastah FCL//20-21/MIL/238 |
TrojanDownloader:O97M/Qakbot.RVC!MTB |
plapointe@camionsdenislussier.com |
smlines.com |
|
Feb 10, 2021 |
INQUIRY - RIO DE JANEIRO PORT - ETA: 19/12 |
TrojanDownloader:O97M/Dridex.SS!MTB |
postmaster@vince.com |
mail-relay.msc.com |
|
Feb 10, 2021 |
Re: TOP URGENT MAERSK DELIVERY |
Trojan:Win32/Ymacco.AA8E |
"Maersk Line" office@anthonyveeder.com |
anthonyveeder.com |
|
Feb 15, 2021 |
[***SPAM*** Score/Req: 08.10/4.4] MAERSK: FINAL PRE-ALERT |
Trojan:MSIL/NanoBot.D!MTB |
“Maersk Notification” 6973711596@xcar.gr |
help.mdaemon.com |
|
Feb 15, 2021 |
Re: Maersk Booking Confirmation |
Trojan:Win32/AgentTesla!ml |
"Maersk Booking Service" mail@trtox.ml |
trtox.ml |
|
Feb 15, 2021 |
status of shipment - shipping documents Air/Sea Logistics |
Trojan:Win32/Azorult!ml |
“Vinay Kashyap (DHL)” 60962@f7203790b.in |
60a459f1d8.com |
|
Feb 16, 2021 |
Re: Maersk Booking Confirmation |
Trojan:Win32/AgentTesla!ml |
"Maersk Booking Service" mail@trtox.ml |
trtox.ml |
|
Feb 16, 2021 |
VSL: MV FORTUNE TRADER - ORDER: TKHA-K77180011B |
Exploit:O97M/CVE-2017-11882!MTB |
"Nguyen Quang (Mr)" ops@vosavungtau.com |
Targets Not Disclosed |
|
Feb 17, 2021 |
mv Ina-Lotte - agency appointment |
Exploit:O97M/CVE-2017-11882.ST!MTB |
“Solar Operations” operations@solar.ru |
alvargonzalez.com |
|
Feb 22, 2021 |
RE: Longstanding Container(s) : 204103842 |
Trojan:Win32/Woreflint.A!cl |
“Thulasi M” dgf.sg.payableinvoices@dhl.com |
dhl.com |
|
Feb 22, 2021 |
RE:JOB NO: 16280-81-82-83-84-85-86 INV. & P. LIST OF NO.2022499 EQ to 2022505 EQ, FOB BY SEA, TOTAL 81+48+28+8+27+32+17 = 241 CARTONS, PORT: HAMBURG BOOKING FORM//4730-0220-102.056 |
Probably Heur.W97Obfuscated |
"Manoj Salve" 5e81f@d375ba752c.com |
5c621a8c5270.com |
|
Feb 22, 2021 |
[External]SHIPPING DOCUMENTS / NAT-UVA 0057 / CONTAINER. MNBU7168737 |
Trojan:MSIL/Stealer.DR!MTB |
info2@alliance22.ru |
sunchemical.com |
|
Feb 24, 2021 |
Arrival notice (Sea shipment * Air shipment: Shipping invoice, B/L, CI, |
Trojan:HTML/Phish.MTL!MTB |
"DHL - Info (DHL/Delivery/Worldwide@dhl.com)" 96f935c3f27@e86c3e2a1.com |
4c6e28732812.com |
|
Feb 24, 2021 |
Arrival notice (Sea shipment * Air shipment: Shipping invoice, B/L, CI, |
Trojan:HTML/Phish.MTL!MTB |
"DHL - Info (DHL/Delivery/Worldwide@dhl.com)" 96f935c3f27@e86c3e2a1.com |
e948985d9c1.org |
|
Feb 24, 2021 |
Arrival notice (Sea shipment * Air shipment: Shipping invoice, B/L, CI, |
Trojan:HTML/Phish.MTL!MTB |
"DHL - Info (DHL/Delivery/Worldwide@dhl.com)" 96f935c3f27@e86c3e2a1.com |
e948985d9c1.org |
|
Feb 24, 2021 |
Arrival notice (Sea shipment * Air shipment: Shipping invoice, B/L, CI, |
Trojan:HTML/Phish.MTL!MTB |
"DHL - Info (DHL/Delivery/Worldwide@dhl.com)" 96f935c3f27@e86c3e2a1.com |
e948985d9c1.org |
|
Feb 24, 2021 |
Arrival notice (Sea shipment * Air shipment: Shipping invoice, B/L, CI, |
Trojan:HTML/Phish.MTL!MTB |
"DHL - Info (DHL/Delivery/Worldwide@dhl.com)" 96f935c3f27@e86c3e2a1.com |
e948985d9c1.org |
|
Feb 25, 2021 |
Mv AOM Julia // Arrival Notice |
Trojan:Win32/Tiggre!rfn |
Kelly Chen 3d25e@6811913.com |
Targets Not Disclosed |
|
Feb 25, 2021 |
Today Vessel LineUp |
Trojan:MSIL/AgentTesla.AM!MTB |
“Vessel Update” 9b8d58b51c58028@5b60b2e1a7419c3c6.br |
30718da8.eg |
|
Feb 25, 2021 |
DOHA PORT RE-DEVELOPMENT PROJECT-CONSTRUCTION OF SPORTS MARINA AND\r\n CONTAINER PARK WORKS |
Trojan:PDF/Phish!MSR |
“Abdelnaser Abu-Eshtayya” 4707b443c2@955497607.com |
955497607.com |
|
February 26, 2021 |
Booking of 1x20\' container against Invoice No. SDE/20-20/12 |
Trojan:MSIL/Kryptik.ST!MTB |
“Celly Cui (DHL CN)” celly.cui@dhl.com |
electroputere.ro |
|
Mar 1, 2021 |
Re: DHL Cargo Delivery |
Trojan:Win32/Woreflint.A!cl |
“DHL Express Cargo” NoReply.ODD@dhl.com |
Targets Not Disclosed |
|
Mar 1, 2021 |
Freight Payment Notification Of 03_01_2021 |
TrojanDownloader:O97M/Dridex.ARJ!MTB |
“MSC MEDITERRANEAN SHIPPING COMPANY (USA) INC.” <Jaden.Nicholson@msc.com> |
asmodei.net |
|
Mar 1, 2021 |
[!!Spam]Ocean Freight overdue invoice Of 03_01_2021 |
TrojanDownloader:O97M/Dridex.ARJ!MTB |
“MSC MEDITERRANEAN SHIPPING COMPANY (USA) INC.” Jaden.Nicholson@msc.com |
asmodei.net |
|
Mar 1, 2021 |
Ocean Freight Payment Notification Of 03_01_2021 |
TrojanDownloader:O97M/Dridex.ARJ!MTB |
“MSC Inc.” Bernard.Burton@msc.com |
backhaus-kutzer.de |
|
Mar 2, 2021 |
Ocean Freight Payment Notification Of 03_01_2021 |
TrojanDownloader:O97M/Dridex.ARJ!MTB |
“msc.com” Nathaniel.Law@msc.com |
mayhew.com |
|
Mar 2, 2021 |
***SPAM*** Freight Payment Notification Of 03_01_2021 |
TrojanDownloader:O97M/Dridex.ARJ!MTB |
“MSC Inc.” Raul.Wright@msc.com |
carou.eu |
|
Mar 2, 2021 |
PORT INFO - M/V SOHO TRADER LOADING 55,000 MT OF STEAM COAL |
Trojan:Win32/Wacatac.B!ml |
“FLAME SA” caf9@00a255c.ch |
dfb80f1afb.net |
|
Mar 3, 2021 |
MAERSK LINE STATEMENT OF ACCOUNT 05 MAR 2020 |
HEUR:Backdoor.Win32.Androm.vho |
“Chen” yan.chen@maersk.com |
cmlog.com |
|
Mar 3, 2021 |
GRANDE APOLLONOS (Ro-Ro cargo) APPAREILLAGE-MYCONOS-GREECE |
Trojan:Win32/Lokibot.SMC!MTB |
“Business Development Officer” ranjan@navi-visaglobal.com |
Targets Not Disclosed |
|
Mar 4, 2021 |
MULTIMAX TBN - PORT INQUIRY FOR DISCHARGE |
Trojan:MSIL/Stealer.DR!MTB |
"mpp.ops@hsshpg.com" mpp_ops@hsshpg.com |
hsshpg.com |
|
Mar 4, 2021 |
MV RELIANCE/AGENCY APPOINTMENT |
Trojan:Win32/Wacatac.B!ml |
“FORTUNE STAR SHIPPING PTE LTD” hello@sgpbusiness.com |
visionit.com |
|
Mar 4, 2021 |
[DHL] SC# 84979926 Cargo Delivery |
Trojan:MSIL/Kryptik.VC!MTB |
“Anunayi Kumari Kar {DHL}” Procurement_Help_IN@dhl.com |
electroputere.ro |
In the above collection, we see malicious actors attempting to use vessel names to try to spoof companies in the maritime supply chain. This week we observed a wide variety of maritime-related subject lines. Some of the new vessel names used this week include “MV Soho Trader” among others. Red Sky Alliance has been monitoring a continuous campaign in which threat actors are impersonating the Mediterranean Shipping Company (MSC) while spreading Dridex malware through malicious email attachments. The attackers are re-using TTP’s to target numerous different targets around the globe in a variety of industries.
Beginning at the end of January, analysts began observing these malicious emails and since then have continued to see the same tactics used multiple times. While it appears, the attackers are spoofing MSC employees at this time, analysts are also monitoring for any malicious emails which appear to be sent by an MSC account which has been taken over.
Although the company was hit by a significant cyber attack last year, Red Sky Alliance is unable to identify any connections between the impersonation campaign and last year’s MSC outage. Red Sky Alliance has not received a response yet from the company regarding these impersonation attacks, but analysts expect that at least some of the targeted businesses use the shipping as part of their supply chain.
The most recent emails follow the exact same patterns analysts have observed since January. These attackers will impersonate MSC employees which do not exist, according to open-source data. They continue to use dozens of unique aliases but not one of the sending emails is seen in open source; indicating that the attackers are using alias names. However, they appear to be using the proper sending email format (first.last@msc[.]com) which shows they have done some measure of reconnaissance on the company.
Commonalities between these emails remain the same:
- All senders impersonate employees or departments at Mediterranean Shipping Company.
- The emails are disguised as invoices or payment notifications (many of them “overdue” to create a sense of urgency in the target).
- The subject lines have a date at the end (mm/dd/yyyy)
- All messages contain a malicious .xlsm file attachment.
- File 1 – “printouts of outstanding as of Monday (MMM_DD_YYYY).xlsm”
- File 2 – “Statement of Account as of Monday (MMM_DD_YYYY).xlsm”
- There are two message bodies used, one just says “redacted” and the other is a description of account charges.
- The attachment contains Dridex[1]
The malicious email attachment titled “Statement_as_of_(DD_MMM_YYY).xlsm” is an updated version of the file reported in last week’s maritime report (WR-21-032-006). Note the .xlsm file extension. This indicates that the spreadsheet will open in Excel with Macros enabled (used to activate the malware).
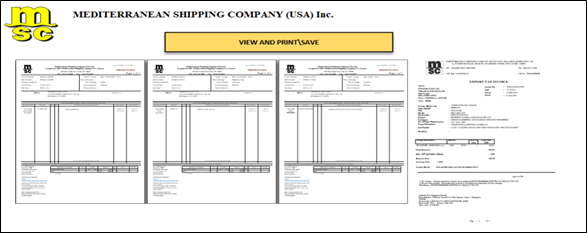
Figure 4 - Malicious .xlsm attachment Open in Excel
In 2021, Red Sky Alliance has already observed supply chain attacks. Maritime employees should be suspicious of any emails using generic greetings such as “Dear Valued Customer” or generic email signatures such as “Credit and Collections Dept.” If attackers are eventually able to bypass webmail filters, their malware is likely to infect at least one unsuspecting user who is curious about the “redacted” email they just received or concerned about an “overdue balance” that they do not owe.
If the targets were to activate this malware on their systems, they would infect their machines with Dridex malware. This malware, which was first observed in 2011, can install other malicious modules on the system. It has also been used to install ransomware on a company network (typically BitPaymer or DopplePaymer). The malware is flexible and has the ability to perform numerous actions under the direction of a command and control server. One of the more interesting aspects of these attacks is the variety in the targeted companies. These attackers are targeting companies across various industries such as manufacturing, entertainment/gaming, and technology.[1] Ransomware - malware
These analytical results illustrate how a recipient could be fooled into opening an infected email. They also demonstrate how common it is for attackers to specifically target pieces of a company’s supply chain to build up to cyber-attacks on the larger companies. Doing so could cause the recipient to become an infected member of the maritime supply chain and thus possibly infect victim vessels, port facilities and/or shore companies in the marine, agricultural, and other industries with additional malware
Fraudulent emails designed to make recipients hand over sensitive information, extort money or trigger malware installation on shore-based or vessel IT networks remains one of the biggest day-to-day cyber threats facing the maritime industry. These threats often carry a financial liability to one or all those involved in the maritime transportation supply chain. Preventative cyber protection offers a strong first-line defence by preventing deceptive messages from ever reaching staff inboxes, but malicious hackers are developing new techniques to evade current detection daily. Using pre-emptive information from Red Sky Alliance-RedXray diagnostic tool, our Vessel Impersonation reports, and Maritime Blacklists offer a proactive solution to stopping cyber-attacks. Recent studies suggest cyber-criminals are researching their targets and tailoring emails for staff in specific roles. Another tactic is to spoof emails from the chief executive or other high-ranking maritime contemporaries in the hope staff lower down the supply chain will drop their awareness and follow the spoofed email obediently. Analysts across the industry are beginning to see maritime-specific examples of these attacks.
Pre-empt, don't just defend
Preventative cyber protection offers a strong first-line defense by preventing deceptive messages from ever reaching staff inboxes, but malicious hackers are developing new techniques to evade current detection daily. Using preemptive information from Red Sky Alliance RedXray diagnostic tool, our Vessel Impersonation reports and Maritime Blacklists offer a proactive solution to stopping cyber-attacks. Recent studies suggest cyber-criminals are researching their targets and tailoring emails for staff in specific roles. Another tactic is to spoof emails from the chief executive or other high-ranking maritime contemporaries in the hope staff lower down the supply chain will drop their awareness and follow the spoofed email obediently. Analysts across the industry are beginning to see maritime-specific examples of these attacks.
The more convincing an email appears, the greater the chance employees will fall for a scam. To address this residual risk, software-based protection should be treated as one constituent of a wider strategy that also encompasses the human-element as well as organizational workflows and procedures.
It is imperative to:
- Train all levels of the marine supply chain to realize they are under constant cyber-attack.
- Stress maintaining constant attention to real-world cyber consequences of careless cyber practices or general inattentiveness.
- Provide practical guidance on how to look for a potential phishing attempt.
- Use direct communication to verify emails and supply chain email communication.
- Use Red Sky Alliance RedXray proactive support, our Vessel impersonation information and use the Maritime Black Lists to proactively block cyber attacks from identified malicious actors.
Related Posts
Maritime Cyber Security & Threats December Week 2
Dryad and cyber partners RedSkyAlliance continue to monitor attempted attacks within the maritime..
Maritime Cyber Security & Threats 4-11 April
Dryad and cyber partners RedSkyAlliance continue to monitor attempted attacks within the maritime..
Maritime Cyber Security & Threats Sep 2020 Week..
Dryad and cyber partners RedSkyAlliance continue to monitor the stark upward trend in attempted..





