15 min read
Maritime Cyber Security & Threats Jul 2020 Week One
By: Dryad Global on July 14, 2020 at 9:43 AM

"Fraudulent emails designed to make recipients hand over sensitive information, extort money or trigger malware installation on shore-based or vessel IT networks remains one of the biggest day-to-day cyber threats facing the maritime industry."
Dryad Global's cyber security partners, Red Sky Alliance, perform weekly queries of backend databases, identifying all new data containing Motor Vessel (MV) and Motor Tanker (MT) in the subject line of malicious emails. Email subject line Motor Vessel (MV) or Motor Tanker (MT) keyword usage is a common lure to entice users in the maritime industry to open emails containing malicious attachments.
With our cyber security partner we are providing a weekly list of Motor Vessels where it is observed that the vessel is being impersonated, with associated malicious emails.
The identified emails attempted to deliver malware or phishing links to compromise the vessels and/or parent companies. Users should be aware of the subject lines used and the email addresses that are attempting to deliver the messages.

|
First Seen |
Subject Line Used |
Malware Detections |
Sending Email |
Targets |
|
Jun 27, 2020 |
RE: Agency appointment for MV VENUS (VENUS/EST/054/20) |
Exploit:O97M/CVE-2017-0199.BK!MTB |
Vicky Lee <vickylee@shippingagency.cn> |
Targets Not Dislcosed |
|
Jun 29, 2020 |
SHIPMENT PAYMENT FOR CARGO AVS-9904SG $70,000USD |
Trojan:MSIL/AgentTesla.SD!MTB |
inam <antonio@mendenhall.gq> |
Targets Not Dislcosed |
|
Jun 29, 2020 |
COSCO SHIPPING LINES - 7223928455 - Document Shipping Instruction/BL |
Trojan:Win32/Ymacco.AAD3 |
COSCO SHANGHAI SHIP MANAGEMENT CO., LTD <coscon@coscon.com |
baltic-sea-forum.org |
|
Jun 29, 2020 |
[DHL] SC# 84979926 Cargo Delivery |
Trojan:Win32/Formbook.VD!MTB |
"Procurement Help (DHL)" <no-replay@mkinn.com> |
Targets Not Dislcosed |
|
Jun 29, 2020 |
SHIPPING DOCUMENTS / CARGO ARRIVAL NOTICE |
Trojan:Win32/Wacatac.C!ml |
MAERSK LINE <mdee_ram@yahoo.com> |
MAERSKLINE.COM |
|
Jul 1, 2020 |
DHL ARRIVAL SHIPMENT PRE-ALERT FOR HCL :CPWMANR2015726 // CONTAINER\r\n NO: MAY0118243 //1X40\'HC
|
Trojan:Win32/Occamy.C6F |
DHL Service <bgv@4ourhome.co.uk> |
dhl.com
|
|
Jul 1, 2020 |
MV ERLYNE - QINZHOU ETA 29/July - Appointment |
Win32.Outbreak |
"Jack Hu" <JHUN@wallem.com.cn> |
wallem.com.cn |
|
Jul 1, 2020 |
CARGO ARRIVAL NOTIFICATION (TNT733918737WA): You Have A Package With Us |
HEUR:Trojan.Win32.Generic |
TNT EXPRESS <service@tnt.com> |
Targets Not Disclosed |
|
Jul 2, 2020 |
RE: MV. SYROS ISLAND - Ship\'s Documents |
Exploit:O97M/CVE-2017-11882.BK!MTB |
"PT. DALIAN PUTRA MARITIM (DPM)" <agency@dalianputramaritim.com> |
Targets Not Disclosed |
|
Jul 2, 2020 |
RE: URGENT!!! SHIPPING DOC BL,SI,INV#462345 // MAERSK KLEVEN V.949E |
Trojan:Win32/Lokibot.SS!MTB |
A.P. Moller - Maersk (Shanghai, Head Office) <eb6bceca@fd8e08.com> |
2010546c.biz |
|
Jul 2, 2020 |
MV JK PIONEER INTEND TO GO TO CHANGZHOU TO DISCHARGE THE COAL |
Trojan:Win32/Wacatac.C!ml
|
"op@tonglishippingpte.com" <ops@tonglishippingpte.com> |
tonglishippingpte.com |
|
Jul 2, 2020 |
PDA MT REGULUS V2006 DISCHARGING 12554MT METHANOL AT JIANGYIN |
Trojan:Win32/Wacatac.C!ml |
"opstracy@163.com" <oprtracy@163.com> |
163.com |
|
Jul 2, 2020 |
RE: mv ASIA RUBY II / DISCHARGING PORT Lianyungang - AGENCY APPOINTMENT |
Trojan:Win32/Wacatac.C!ml |
"ITIRO CORPORATION, OPERATIONS" <operation@itiro-corp.com> |
itiro-corp.com |
|
Jul 2, 2020 |
RE: MV Selenga // LIANYUANGANG- dischg cgo |
Trojan:Win32/Wacatac.C!ml |
Darore Shpg//Chen <shpg@darore.com> |
darore.com |
|
Jul 2, 2020 |
RE: MT OCEAN CHEMIST / V.2004B / DUE SINGAPORE OR TANGJUNG PELEPAS,\r\n MALAYSIA FOR LOADING - AGENT APPOINTMENT |
Trojan:Win32/Wacatac.C!ml |
caf9@3cabc1a5e50699.com |
Targets Not Disclosed |
|
Jul 3, 2020 |
MV JK PIONEER INTEND TO GO TO CHANGZHOU TO DISCHARGE THE COAL |
Trojan:Win32/Wacatac.C!ml |
"op@tonglishippingpte.com" <ops@tonglishippingpte.com> |
tonglishippingpte.com |
|
Jul 3, 2020 |
[WARNING - ENCRYPTED ATTACHMENT NOT VIRUS SCANNED] RE: REQUEST FOR QUOTATION - M.V. OMNI TIGRIS DRY DOCKING |
Trojan:Win32/Tiggre!rfn |
"Ronnie M. Celio" <guw_std5@a-c-s.kz> |
Targets Not Disclosed |
|
Jul 3, 2020 |
MV GENCO RESOLUTE/ DISPORT AGENCY NOMINATION/ |
Trojan:Script/Foretype.A!ml |
cfdb43@6934fa335bbd.CN |
a694174ef.com |
|
Jul 3, 2020 |
m/v ocean confidence additional store 20H019 |
Trojan:Win32/Wacatac.C!ml |
"Liping wang" <supply100@oceanlongevity.com.hk> |
oceanlongevity.com.hk |
|
Jul 3, 2020 |
Mv. DREAM STAR //CTM REQUEST; ETA 9th JULY 2020 |
Trojan:Win32/Wacatac.C!ml |
"NMT China Co., Ltd." < Jocelyn_wang@nmtshipping.com> |
nmtshipping.com |
|
Jul 3, 2020 |
SHIP ARREST/PENDING PDA |
Trojan:Script/Oneeva.A!ml |
Business and Property Court <41289efd29c65c@771a3e9f6c8.uk> |
30718da8.eg |
|
Jul 3, 2020 |
Maersk Line Order Completed
|
Trojan:Script/Oneeva.A!ml |
"Maersk Line"<793da9dcbe4@6e661917114da30873.com> |
Targets Not Disclosed |
Top 5 Malicious Maritime Subject Lines
|
Subject Line used |
Email Sender using Subject Line |
Times seen |
|
Re: Purchase Order |
"Chen Leo" office@coucsosdari.com |
11 |
|
M/T OCEAN CHEMIST NOMINATION / PDA REQUEST |
"Platinum Marine Bunker Co. Ltd."<caf9@3cabc1a5e50699.com> |
6 |
|
RE: mv ASIA RUBY II / DISCHARGING PORT Lianyungang - AGENCY |
"ITIRO CORPORATION, OPERATIONS" <operation@itiro-corp.com> |
5 |
|
COSCO SHIPPING LINES - 7223928455 - Document Shipping Instruction/BL |
COSCO SHANGHAI SHIP MANAGEMENT CO., LTD <coscon@coscon.com |
5 |
|
SHIPMENT PAYMENT FOR CARGO AVS-9904SG $70,000USD |
inam <antonio@mendenhall.gq> |
5 |
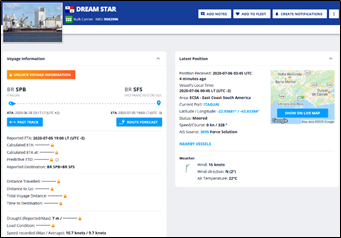
In the above collection, we see malicious actors attempting to use vessel names to try to spoof companies in the maritime supply chain. This week we observed a wide variety of maritime-related subject lines. Some of the new vessel names used this week include “MV Ocean Confidence” and “MV JK Pioneer” among others. “Maersk Kleven” was seen in the malicious email subject lines this week after not being observed last week. This vessel has been part of the subject line for at least 9 attack attempts in just the past 90 days. With 6418 twenty-foot equivalent units (shipping container space) onboard, there are numerous companies using this vessel as part of the supply chain. The vessel recently departed Genova, IT and Red Sky Alliance will continue to monitor malicious activity leveraging the vessel’s name.
Analysts observed subject line “SHIPPING DOCUMENTS / CARGO ARRIVAL NOTICE” being used in a malicious email this week. This is a generic enough subject line that it can be used on multiple different companies without the need for editing. Subject lines like these are often used for malware spam campaigns. If the attacker sends out a hundred emails and is only successful on a few of them, it is still a lower-risk, higher-return attack.
Notably, the attacker attempts to impersonate an employee at the company they are targeting. The malicious email sender is “MAERSK LINE <mdee_ram@yahoo.com>.” Notice how the email alias is “Maersk Line,” however the sender email is a generic Yahoo address. Attackers can easily spoof the email sender alias which will trick users who are not paying attention to the sending email.
Although the exact target is unclear, the email is targeting a user on the Maerskline[.]com domain. Training and implementation of good security policies will help make users aware of how to spot the actual sending address of a malicious email.
The message body claims the sender has been asked to “dispatch one of (the recipients) shipments” and to open the attached documents for tracking. The attached files are contained in a zip file called “MAERSK LINE.zip.” When the user decompresses the zip file, there is a “MAERSK LINE.exe” executable file which is actually Fareit password stealing malware. This malware is capable of stealing and exfiltrating the victim’s sensitive information including usernames and passwords.
Analysts observed a malicious email subject line, “RE: URGENT!!! SHIPPING DOC BL,SI,INV#462345 // MAERSK KLEVEN V.949E.” After a brief break from use as a malicious email subject line, the “Maersk Kleven” ship name is being seen again this week. One common method employed by the attackers this week is to use the phrase “urgent” and “re:” to indicate an ongoing conversation which requires an immediate reply.
The email listed as the sender " A.P. Moller - Maersk (Shanghai, Head Office) <eb6bceca@fd8e08.com>” indicating the attacker is attempting to impersonate A.P. Moller Maersk. Shanghai is the busiest port in the entire world, so it is unsurprising to see attackers impersonating one of the largest shipping companies from the largest port in the world. As the sending address is obfuscated, it is unclear if the attacker was attempting to impersonate a specific employee at the massive shipping port.
The message body of the email is redacted further obscuring the sender and target. All of the malicious emails, with the exception of one, list “A.P. Moller – Maersk” as part of the sender alias. The exception was described in previous reporting (TR-20-125-006). However, some choose to add the “(Shanghai, Head Office)” portion which would further entice targets who use Shanghai as part of their supply line.
Attached to the email is a file named, “Shipping Doc_Maersk Kleven V.949E.gz.” This is a gzip file which, when opened, deletes itself when downloaded. When the targeted user clicks the malicious file, it will drop Lokibot malware. First publicized in 2015, Lokibot trojan malware has the ability to infect Windows systems, steal, and then exfiltrate sensitive information, including but not limited to usernames and passwords. Red Sky analysts have observed most bad actors leveraging this vessel’s name sending Fareit and Lokibot malware while exploiting CVE-2017-11882.
These analysis results illustrate how a recipient could be fooled into opening an infected email. Doing so could cause the recipient to become an infected member of the maritime supply chain and thus possibly infect victim vessels, port facilities and/or shore companies in the marine, agricultural, and other industries with additional malware.
Fraudulent emails designed to make recipients hand over sensitive information, extort money or trigger malware installation on shore-based or vessel IT networks remains one of the biggest day-to-day cyber threats facing the maritime industry. These threats often carry a financial liability to one or all those involved in the maritime transportation supply chain. Preventative cyber protection offers a strong first-line defence by preventing deceptive messages from ever reaching staff inboxes, but malicious hackers are developing new techniques to evade current detection daily. Using pre-emptive information from Red Sky Alliance-RedXray diagnostic tool, our Vessel Impersonation reports, and Maritime Blacklists offer a proactive solution to stopping cyber-attacks. Recent studies suggest cyber-criminals are researching their targets and tailoring emails for staff in specific roles. Another tactic is to spoof emails from the chief executive or other high-ranking maritime contemporaries in the hope staff lower down the supply chain will drop their awareness and follow the spoofed email obediently. Analysts across the industry are beginning to see maritime-specific examples of these attacks.
Pre-empt, don't just defend
Preventative cyber protection offers a strong first-line defense by preventing deceptive messages from ever reaching staff inboxes, but malicious hackers are developing new techniques to evade current detection daily. Using preemptive information from Red Sky Alliance RedXray diagnostic tool, our Vessel Impersonation reports and Maritime Blacklists offer a proactive solution to stopping cyber-attacks. Recent studies suggest cyber-criminals are researching their targets and tailoring emails for staff in specific roles. Another tactic is to spoof emails from the chief executive or other high-ranking maritime contemporaries in the hope staff lower down the supply chain will drop their awareness and follow the spoofed email obediently. Analysts across the industry are beginning to see maritime-specific examples of these attacks.
The more convincing an email appears, the greater the chance employees will fall for a scam. To address this residual risk, software-based protection should be treated as one constituent of a wider strategy that also encompasses the human-element as well as organizational workflows and procedures.
It is imperative to:
- Train all levels of the marine supply chain to realize they are under constant cyber-attack.
- Stress maintaining constant attention to real-world cyber consequences of careless cyber practices or general inattentiveness.
- Provide practical guidance on how to look for a potential phishing attempt.
- Use direct communication to verify emails and supply chain email communication.
- Use Red Sky Alliance RedXray proactive support, our Vessel impersonation information and use the Maritime Black Lists to proactively block cyber attacks from identified malicious actors.
Related Posts
Maritime Cyber Security & Threats Aug 2020 Week..
Dryad and cyber partners RedSkyAlliance continue to monitor the stark upward trend in attempted..
Maritime Cyber Security & Threats Aug 2020 Week..
"Fraudulent emails designed to make recipients hand over sensitive information, extort money or..
Maritime Cyber Security & Threats Sep 2020 Week..
Dryad and cyber partners RedSkyAlliance continue to monitor the stark upward trend in attempted..





